3 steps to prevent the next Gatwick incident

Over 1,000 flights were disrupted during peak holiday season after a drone was spotted near Gatwick airport. Image: REUTERS/Peter Nicholls
From 19 December to 21 December 2018, hundreds of flights were cancelled at Gatwick Airport near London, England, following 67 reports of drone sightings close to the runway.
The incident negatively impacted about 140,000 passengers and disrupted over 1,000 flights during peak holiday travel. Reactions by UK police, military, and government officials exposed a lack of preparation in responding to unlawful drone incursions.
All in all, a spokesperson for Gatwick Airport estimates the total cost to the airport and airlines at £20 million in lost revenue. As of writing this article, the perpetrator, or perpetrators remain at large, and another suspected drone sighting affected Heathrow Airport on 8 January.
Unfortunately, many airports, air navigation service providers (ANSPs), civil aviation authorities (CAAs) and governments around the world are not yet prepared to respond to drone incursions and are understandably worried that they could be affected by similar incidents.
Many early reactions have called for counter-UAS (unmanned aerial system) technology as the most effective solution for prevention. Of course, there is a key role for these systems in airport safety, but they are a last resort against criminals. Without the ability to remotely identify good actors from bad ones, these counter systems will be constrained as drone operations scale.
Thankfully, a lot can be done today to reduce the risks of drone incursions to a manageable level that only requires basic regulation and technology. Here are three concrete steps that airports and aviation authorities can take to keep airports safe from unwanted and/or criminal drone activity.
Step 1: Implement a registration mandate with easy-to-use technology
Airspace authorities should establish clear regulations that require all drone operators to register themselves and their aircraft along with a simple, streamlined process for doing so.
Implementing a digital registration system is relatively easy – drone operators can enter name, contact, and aircraft details on an internet-enabled device, which populates a secured registration server, that also attest identities and authenticate users. Access to registration data is managed by authorized personnel, with appropriate personally identifiable information (PII) protections in place.
Mandatory registration can also require that a drone operator self identify in order to get authorized access to fly in controlled airspace near airports. Registered operators are responsible actors who have demonstrated intent to operate in compliance with regulations.
Step 2: Enforce civil aviation regulations with a UAS Traffic Management (UTM) system
Popular drone manufacturers already implement geofencing options, and firmware updates to meet national airspace regulations. In practice, geofencing prevents a drone from flying in restricted, controlled and other unsafe airspace, which helps ward against illegal drone operations by careless and clueless operators.
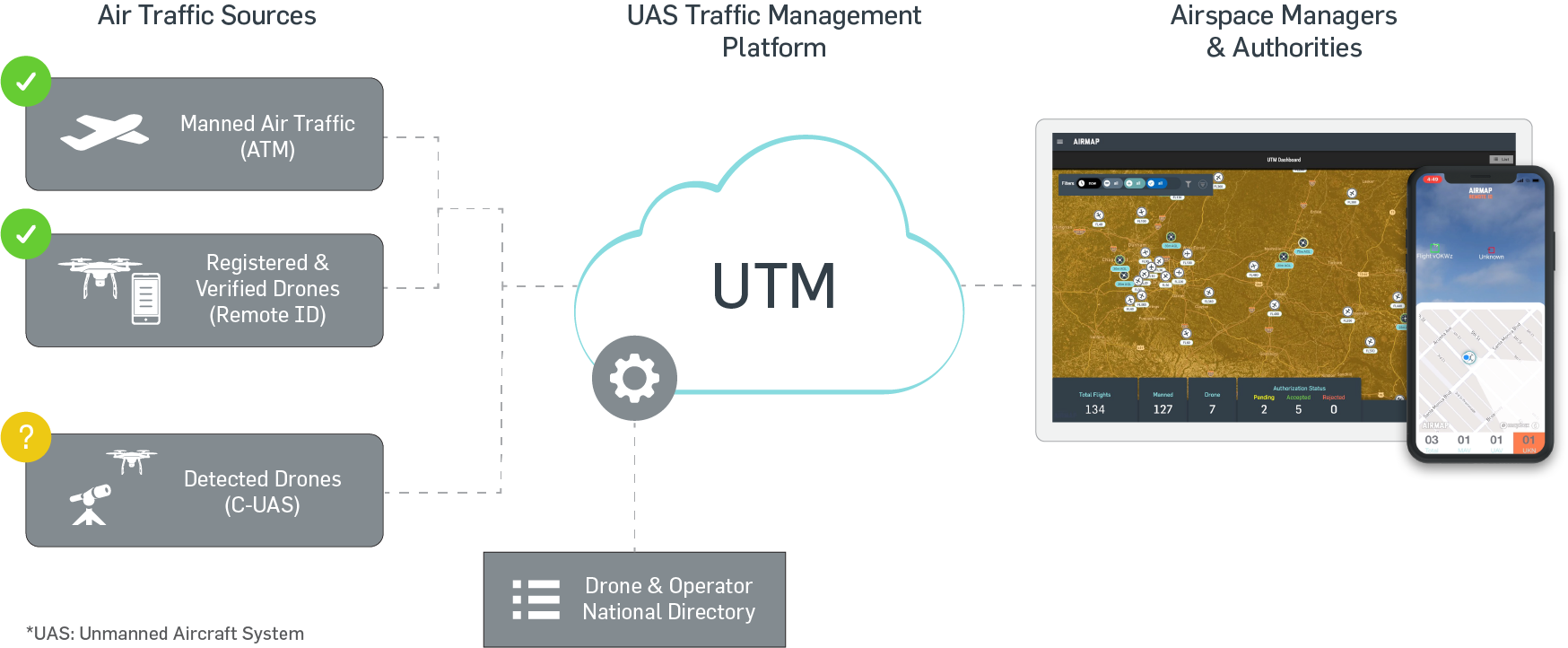
Geofencing can be “unlocked” for authorized drone operators, such as airport maintenance staff or law enforcement operators, by connecting to an Unmanned Traffic Management (UTM) system with services and procedures designed to support safe, efficient and secure access to airspace for drones. These services include registration, flight planning, geofencing, airspace authorization, conformance monitoring, telemetry, deconfliction, and remote identification, among others.
The right UTM system analyzes operator details, flight path information, real-time air traffic positions, and more, to enable airspace authorities to grant permission-based access to drone operators in controlled airspace, either manually or programmatically as already implemented by the Federal Aviation Administration Low Altitude Authorization and Notification Capability (FAA LAANC) programme. The result is enablement of safe drone operations while controlling against non-compliant or illegal activity.
With all “good actors” participating in the UTM system, aviation authorities can visualize, monitor, and track real-time manned and unmanned aircraft telemetry for deconfliction. Participating drone operators can be remotely identified by their aircraft, flight path, and/or registration details and can be contacted directly for risk mitigation.
Step 3: Combine UTM with counter-UAS system for a complete picture of an airspace operating environment
Intentional bad actors that are not registered are not included in the UTM system and do not follow the appropriate authorization procedures to access controlled airspace. These illegal operators may also hack their drones, unlocking geofencing, or spoofing their location.
In these instances, the integration of counter-UAS (C-UAS) technology into the UTM system provides the ability to identify all aircraft movements within the controlled airspace. Information related to any aircraft detected by C-UAS is exchanged with the UTM system and remotely identified as either collaborative (registered) or non-collaborative, requiring intervention.
Much of the reaction to the Gatwick incident has centred on counter-UAS technology as the answer to all illegal drone operations. But as drone operations near airports scale with enterprise demand, C-UAS alone will not be sufficient in determining whether a drone operation requires intervention because not all drone operations at airports are unlawful. Detection must be coupled with UTM intelligence to adequately inform, and ensure the safety and smooth operations of all airports.
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Drones
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on Emerging TechnologiesSee all
Silje Ditlefsen Zanni and John Dutton
April 22, 2026






