Why the evolution of blockchain reliability is critical to protecting your digital assets

Image: Photo by Alina Grubnyak on Unsplash
- The existence of digital assets is dependent on the reliability of the blockchain.
- Understanding key vulnerabilities can help better assess blockchain reliability.
Much has been said in recent months about blockchain technology and the security and reliability its networks can offer. Given the fact that risks and controls may look different in the blockchain ecosystem, especially when supporting a company’s financial reporting process, protecting digital assets deserves further exploration.
Why effectively-designed blockchains are key
In traditional contexts, an asset can be observed or tracked via source documents or physical observation. However, digital assets exist as a digital record maintained on a blockchain, often with no further physical representation. Digital assets comprise a broad range of items represented as binary data with usage rights and can range from certificates to crypto-assets. If the blockchain breaks down, a company may not be able to assert through their financial reporting that the digital asset exists. Therefore, existence of digital assets is dependent on the reliability of the blockchain (i.e., blockchain technology and support network).
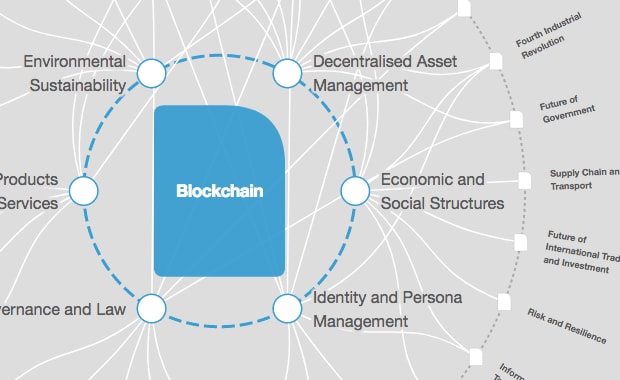
How is the World Economic Forum promoting the responsible use of blockchain?
Identifying vulnerabilities
A reliable blockchain should have an effective design for its intended purpose - to properly record a digital asset’s creation or transfer with the following elements:
- Initiated or observed through deployment services
- Agreed upon by the network with a consensus protocol
- Maintained on the distributed ledger by network enablers
- Cryptographically secure
- Supported by the community of developers
It may be difficult to conclude a digital asset actually exists when one or more of these elements is vulnerable to breaking down. Below we explore some of these vulnerabilities and what companies can do to enhance their internal controls over blockchain reliability.

Deployment services are those technology and service providers that allow individuals and businesses to interact with a digital asset. Examples include blockchain explorer software, digital wallets, custodial services and exchanges. There are variations in the types of deployment services and vulnerabilities, however those that offer data services (e.g., blockchain reader, analytics) present unique challenges to existence. As part of supporting that a digital asset exists, one would look to its representation on the blockchain.
Within financial reporting, a company may utilize a service to directly read and report on the status of its digital assets (e.g., type, quantity, historical transactions). The information obtained by the company may have been sourced from the blockchain, but it may be incomplete or inaccurate through errors in the software or manipulation. Companies may look to obtain a service auditor’s report from the data service provider that would support reliability of its internal controls.
Consensus protocol
The objective of the consensus protocol is to ensure that the blockchain network’s node operators will reach the same conclusion about the validity of transactions. A consensus protocol includes rules for: designating which node operator(s) determines which transactions should be accepted in the next block of recorded transactions as “true”; operating the incentive model that encourages participation and discourages bad actors; and equal sharing of information for a common truth of facts among node operators.
Reliability of the blockchain records may be vulnerable when a blockchain’s open source software contains errors or bugs. Critical vulnerabilities have been uncovered within the source code of various blockchains that if exploited could have triggered an unintentional hard fork (i.e., split of the blockchain). Unfortunately, service auditor reports are not available for public blockchains and it may not be feasible or effective for companies to perform their own source code reviews. Companies may consider ways to assess new developments and reports of vulnerabilities in code versions.
Network enablers
The network enablers comprise the blockchain node operators that perform the essential tasks of validating new blocks and mining (specific to proof-of-work blockchains) for the network. Most node operators are honest and seek to support the reliability of blockchain records in pursuit of the consensus protocol’s incentive model. However, there are a variety of attack vectors against blockchain networks depending on how the consensus protocol is designed. There have been attacks against blockchain networks that resulted in transactions being removed, reorganized and replaced. The reliability of the blockchain records seemingly become less reliable with fewer node operators in a blockchain network. Implementing security policies (e.g., notarizing blocks, penalty systems) may be considered during a blockchain’s lifecycle, but these tend to reduce speed of transaction processing. Companies may consider employing their own monitoring activities to understand and respond to risks.
Security
The security of blockchain technology occurs when data is cryptographically linked through the chain of blocks. This key feature of blockchain also poses challenges to reversing bad transactions or fixing unreliable smart contracts caused by user error or poor design. Companies may need to rely on the internal controls operated by smart contract owners and consider employing their own internal controls around initiating transactions and recovering unintended transactions with smart contracts.
Community of developers
Each public blockchain is supported by a community of developers who may be individuals, groups of individuals and formal organizations. Their effectiveness is key for blockchain reliability. The community promotes their blockchain adoption, responds to feedback from users and node operators, performs research and development for the source code, organizes version updates, and performs source code testing and monitoring. The community is often organized around a non-profit foundation that provides governance over the blockchain. While commonly known digital assets may have active foundations, there are many abandoned digital assets where the foundation dissolved or failed to form. Companies may consider employing their own monitoring activities to assess a community or foundation’s effectiveness, integrity, talent and version updates.
"A reliable blockchain should have an effective design for its intended purpose - to properly record a digital asset’s creation or transfer."
”Unique risks and challenges emerge when considering financial reporting in this ecosystem. This article has only begun to touch on challenges with the reliability of blockchain technology and its records – a key consideration for assessing if a company’s digital assets even exist (the World Economic Forum's Blockchain Deployment Toolkit, launched last month, discusses these considerations in more detail). Still, it is increasingly clear that each of the elements that support reliability deserve further analysis but many questions remain as it relates to these systems of internal controls. Certainly, authoritative bodies around the world are proposing frameworks, issuing guidance and providing feedback for companies and service providers. Companies will only fully benefit from adopting digital assets by being proactive and savvy in meeting these complex challenges with the help of effectively designed internal controls over financial reporting.
Contributors to this report include: Tim Davis, Risk & Financial Advisory Principal, Deloitte & Touche LLP; Brian Hansen, Audit & Assurance Partner, Deloitte & Touche LLP; Peter Taylor, Audit & Assurance Senior Manager, Deloitte & Touche LLP
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Blockchain
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.