Quantum computing could be a major challenge for bitcoin

Blockchain and quantum computers are exciting new technologies, but one could be the others downfall. Image: REUTERS/Dado Ruvic
A Different Kind of Computing
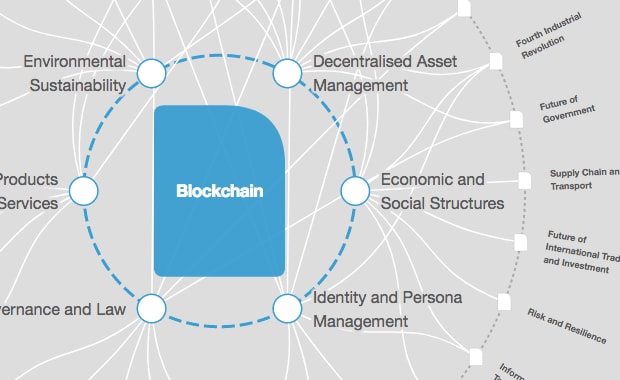
While much of the world is captivated by the meteoric rise of bitcoin’s value, others are focused on the technology behind the cryptocurrency: blockchain. The decentralized digital ledger tech is built upon a peer-to-peer network, and it is far more secure than the centralized systems used by traditional banks and financial institutions. However, another revolutionary technology is now threatening Bitcoin’s security.
In a recently published paper, Divesh Aggarwal and his colleagues from the National University of Singapore (NUS) examined how quantum computers could undermine and even exploit Bitcoin’s security protocols.
As explained by the MIT Technology Review, these protocols use algorithms to turn data into mathematical functions. Every transaction is recorded into “blocks” using these functions as part of the computationally demanding work of cryptocurrency mining.
These cryptographic protocols make cracking a blockchain using today’s computers practically impossible, but the system does have weak points quantum computers could exploit.

Cryptography Gets Busted
For their paper, Aggarwal and his colleagues examined how quantum computers could break through Bitcoin’s security in two ways: by mining more than classical computers can and by cracking Bitcoin’s cryptographic keys.
If a miner controls more than 50 percent of the computational power on a blockchain network, they can use that majority control for malicious activity. The researchers found that the application-specific integrated circuits (ASICs) currently used by most cryptocurrency miners should be able to maintain a speed advantage over quantum computers for the next 10 years, so miners likely won’t be able to use quantum systems for nefarious purposes in this manner for at least a decade.
As for cracking today’s cryptographic keys, part of Bitcoin’s security protocol involves every bitcoin owner possessing two encryption keys: a private one and a public one. The latter can be easily generated using the former, but the reverse is far more difficult. An owner’s signature is verified without revealing the private key using a technique called elliptic curve signature scheme.
While conventional computers don’t possess the necessary computational power to derive a private key from a public key, quantum computers could do it rather easily. “The elliptic curve signature scheme used by Bitcoin…could be completely broken by a quantum computer as early as 2027,” Aggarwal and his colleagues wrote.
Cryptography Gets Boosted
This security threat isn’t unique to Bitcoin. Just about everything on the internet and every computer system with a modicum of security uses the same cryptographic principles. To that end, quantum computers put anything using today’s encryption methods at risk.
“[T]here is little doubt that the power of quantum computing could be used to ‘crack’ current encryption methods,” William Hurley, the chair of the Quantum Computing Standards Workgroup of the Institute of Electrical and Electronics Engineers (IEEE), told Futurism.
“Encryption methods like RSA are based on the simple premise that factoring large numbers is computationally unattractive,” said Hurley, who has previously written about the threat quantum computers pose to today’s encryption methods. “RSA and other encryption methods essentially make it so time and resource intensive that it becomes undesirable to invest in breaking the encryption. With the advent of quantum computers, the factoring of these two large numbers now becomes more of a reality.”
Quantum computers could potentially become so powerful they require their own kind of cryptography, but that doesn’t mean Bitcoin and today’s encryption methods must be scrapped entirely. With some reworking, they could be made more secure.
For starters, Hurley suggests doubling or tripling the length of cryptographic keys. “Doubling the length of the encryption key is even more effective in a symmetric encryption scheme,” he said. “Quantum computers could use Grover’s Algorithm to break symmetric keys in quadratic time, but that’s not nearly fast enough to overcome a longer key.”
According to MIT Technology Review, Bitcoin doesn’t have any plans to revise its current security protocols just yet, but with usable quantum computers still a decade or two away, cryptocurrency platforms have time to reconsider their encryption methods.
“It’s easy to romanticize quantum computing. And while the technology is closer than you think, it’s not magic,” said Hurley. “It will not be the end of encryption, as many propose.”
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Blockchain
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on Emerging TechnologiesSee all
Dr Gideon Lapidoth and Madeleine North
November 17, 2025