We must rethink and repurpose cybersecurity for the COVID-19 era

The shift to working from home is one of the changes forcing a rethink of cybersecurity approaches Image: DarkworkX on Pixabay
- COVID-19 has changed how people work, and cybersecurity needs to reflect this new normal.
- As networks and cloud environments stretch to accommodate the new reality, edge security strategies must be extended.
- The challenge here is not new technology, but old mindsets.
For businesses all over the world, adjusting to the new realities created by COVID-19 has been an incredible challenge. From a technology perspective, the crisis has forced companies to make massive changes - from meeting the needs served by suddenly shuttered workspaces, to scaling the tools required to connect entire workforces now isolated at home.
For IT teams that are already stretched thin, just getting the tactical tools and techniques needed for business continuity up and running has been a massive undertaking complicated by intense time pressures. But all of that was just the beginning. To protect and strengthen those efforts, we must now go beyond initial tactical approaches to adjust underlying security strategies and workplace philosophies as well.
For many companies, the biggest obstacle will not be the technology; it will be the ability to recognize that these short-term disruptions are here for the long-term, if not actually permanent. It is also critical that we begin now to seize the opportunity presented by these cultural and technological shifts to embrace a more strategic approach to security. Just as it has been very difficult for some companies to embrace the principles and practices of working remotely, some organizations may still attempt to cling to a network model that doesn’t really reflect the form or function of how their cloud and networks must now operate.
But the fact is, the primary organizing concept in many organizations’ network strategy — that there is a centre, and then there is everything else — is gone. To adjust, the principles and practices we use to secure what we once called the edge must now be adapted to and scaled across the entire network.
For many of us, this is not a new necessity. For years, security professionals have advised companies to adjust their security strategy to secure the remote edge, not just the traditional core network perimeter, and to employ security-driven networking. Even so, nobody could have predicted just how quickly and fundamentally those changes would be forced on us in the wake of COVID-19. We may never entirely go back to what we knew as normal. And perhaps the most dangerous thing we could do now is to leave our expanded edge strategy out on the edge.
Moving forward, edge security, cloud security and network security must be synonymous. A security-driven networking strategy that blends the entire distributed network into a single, coherent solution is no longer optional – it will be an imperative. Fusing networking, the cloud and security must be the foundational structure of not only what is done now, but also of any innovations to come.

We have already begun to see solutions designed to define and secure networks with software, enabling organizations to approach security, the cloud and networking with a single, unified strategy for all edge computing. Many companies that had already invested in integrating their software-defined networking in a wide area network (SD-WAN), next-generation firewall (NGFW) technology and multi-cloud deployments into a unified system were in a much better position to pivot to the demands of a totally restructured workplace. But now that remote networks have taken a primary position, organizations must extend that strategic edge approach throughout the network and out to the cloud to make sure it is consistent, integrated and secure.
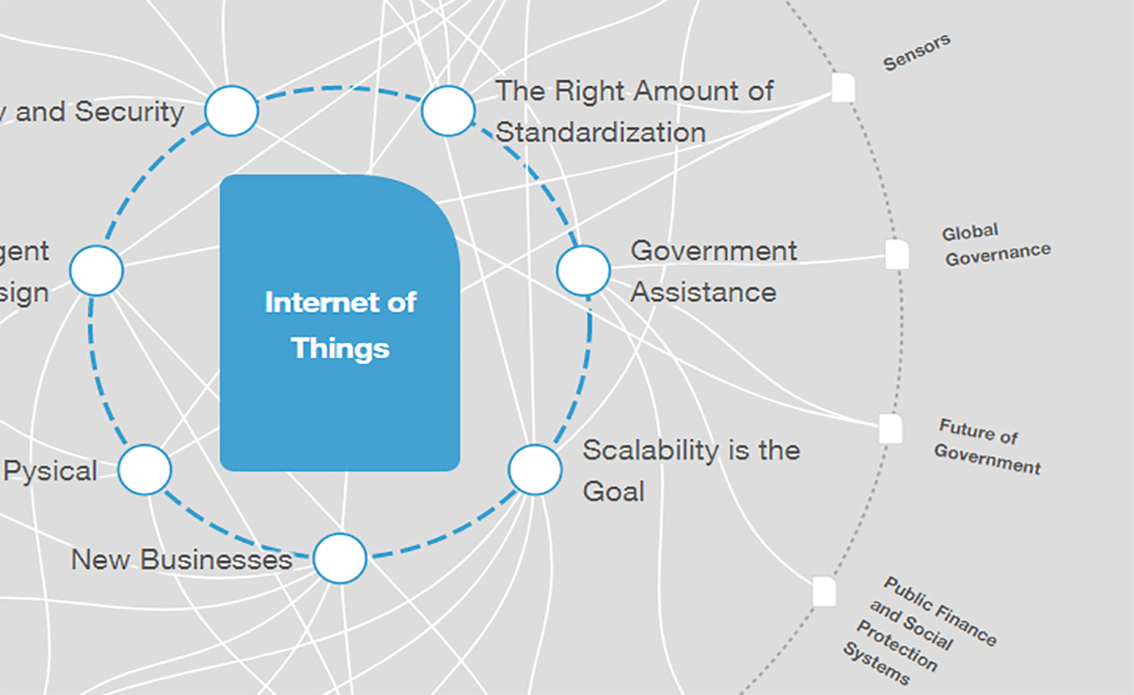
These changes may seem painfully sudden and sweeping. But the truth is we were already rapidly running out of runway. It was inevitable that security would have to follow data, and data has been moving to the edge and being distributed across an expanding network for some time now. Even without a global lockdown separating us physically, the proliferation of IoT — which includes billions of highly vulnerable access points with code not developed with security-first in mind — was always going to blow a gaping hole in networks eventually. Suddenly, eventually is now.
How the Forum helps leaders understand cyber risk and strengthen digital resilience
There is no choice now but to move forward. Though challenging, we are being given an opportunity to create the type of connectivity and security we have long known we would need, but have been avoiding. That may be one bright outcome from this terrible crisis, but only if organizations can focus quickly and execute this strategy thoroughly.
Thankfully, the technology to achieve these solutions is available. Security-driven networking that utilizes AI to drive efficient, integrated solutions that span remote access and across dynamically distributed networking and cloud environments allows companies to maintain the pace of business. But it will also enable IT teams to focus on higher priority challenges, such as segmentation and authentication, to protect organizations as well as prepare for the opportunities of 5G, ultra-rich media and smart solutions, including smart vehicles, buildings and cities.
We know that we must rely on digital connections more than ever, it is critical that we ensure that those connections are safe, fast, scalable, and strong throughout our networks. Whether we like it or not, whether we are ready or not, we have been pushed to the edge. The only question now is how quickly organizations can extend their networking strategy so they can remain safe there.
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Internet of Things
Related topics:
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on CybersecuritySee all
Helmut Reisinger
December 17, 2025