Cybersecurity's visibility problem: if a self-driving car crashes, whose responsibility is it?

The autonomous car dilemma is one example of the difficulty of assigning responsibility across interconnecting digital systems. Image: Getty Images/iStockphoto
• Ubiquitous connected computing and complex supply chain pose new security challenges.
• Cybersecurity processes need system-wide- and inter-system visibility to identify threats.
• The multitude of different devices and security standards currently hinder this visibility.
The critical technology transformations on which future prosperity relies – ubiquitous connectivity, artificial intelligence, quantum computing and next-generation approaches to identity and access management – will not just be challenges for the security community. They have the potential to generate new and systemic risks for the global ecosystem, and at this stage their full impact is not well understood.
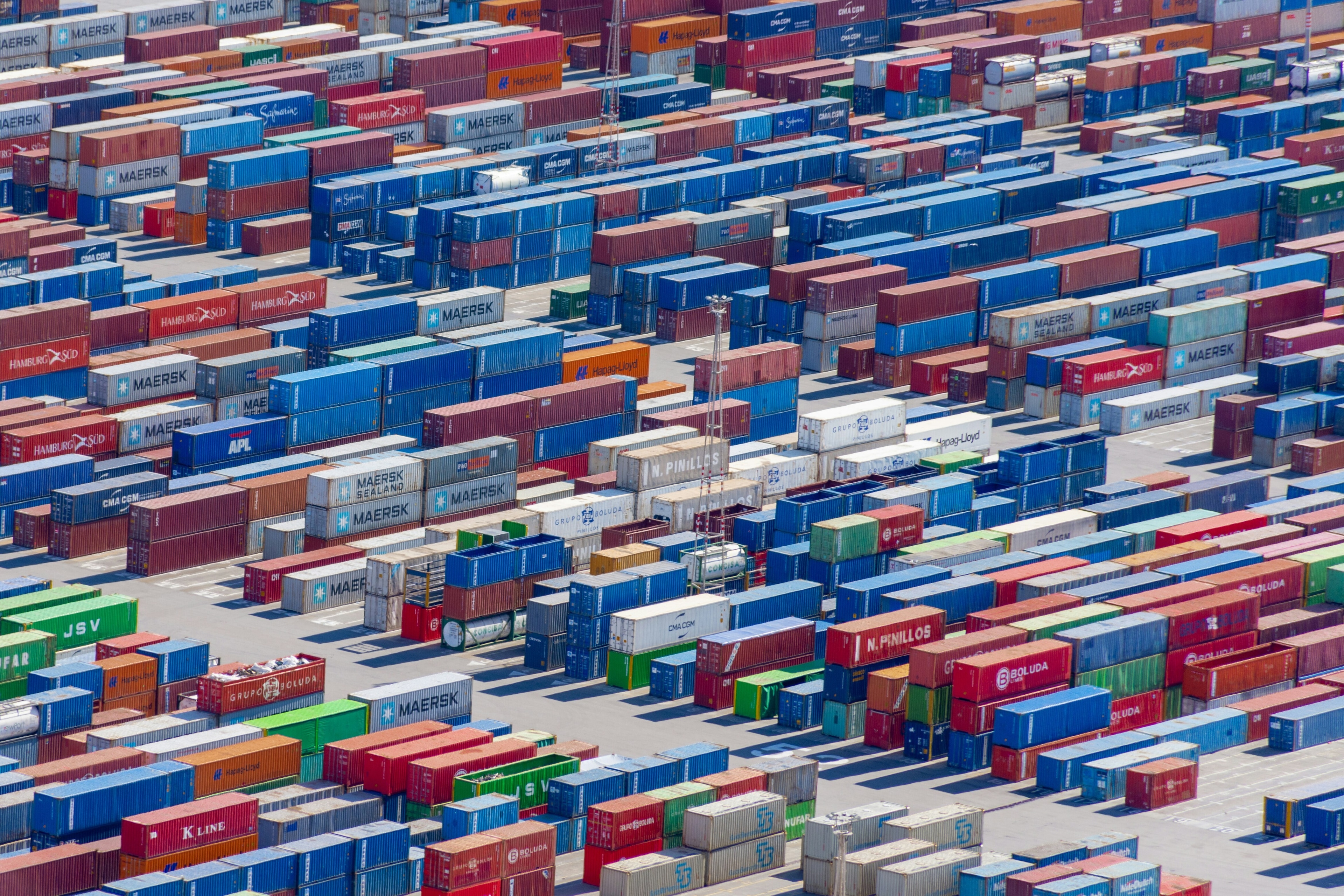
If we are to realize all the great benefits that come from ubiquitous connected computing, there are some unique new security challenges – 5G security being just one – that business leaders must be confident we can overcome. Increasingly interconnected digital processes mean increasingly complex supply chains. It’s both a blessing and curse, as these new digital connections enable new business opportunities, but with them comes as many unknowns and risks.
The World Economic Forum Future Series initiative convened global experts to work together on identifying the systemic risks emerging from these new technologies. One of its key insights is that experts can quantify systemic risks, but when it came to who owned the responsibility it is conspicuously unclear. This is the major issue the global community needs to address, as without clear ownership and responsibility, security issues remain unfixed. This requires us to address the visibility challenge.
Understanding the security risks
We are already on the path to massive change. Businesses are moving at pace away from traditional data centres that privately hold their intellectual property and other sensitive business information on the cloud in order to leverage its key ability to connect and correlate different data so they are great than the sum of their individual parts. The distributed computing models that the cloud and edge computing provides eschew multiple paths of digital processing for real-time, complex meshes of data that enable connected cars and smart cities. Just stop to think about how many sources of data a connected car can process coming from multiple sources in parallel. We have already seen how one wrong or misinterpreted data set can have a catastrophic impact.
The Future Series report outlines the example of where responsibility might lie if an autonomous car crashes with another: Is it the radar system, the software that controls it, the communications software between the two cars, the main software system controlling the car’s safety, the speed or quality of the connection between the cars? The list is potentially endless. For business leaders, this example is one of many where they will need to decide whether the business will either accept, manage or expect a third party to manage the risks. And in cybersecurity you need to be able to see what the risk is.

Two other technical trends highlight the problem:
Increasing Use of Edge Devices/IoT: Think about the scenario where a $5 wireless-enabled IoT temperature sensor and an MRI scanner costing over $500,000 are on the same communications network. These do not come with the same investment in cybersecurity, such as reliable code, security patching and using secure credentials. As such, smart network visibility tools will be required to help define separation (or, as it’s more commonly known, segmentation) to group together things that should talk to each other, and apply security controls aligned to the risks of these grouped devices.
Data: Connecting things enables limitless new possibilities and business opportunities. However, privacy laws such as GDPR and CCPA often require that personal information can only be shared within certain stipulations, such as consent and purpose. To share personal data legally within these contexts, you will need to know what things on your network are collecting personal data and define acceptable sharing controls, which means understanding the things and the traffic that is allowing them to communicate.
When it comes to data visibility, supply chains are critical and increasingly complex. This in turn will require an infrastructure chain; by which I mean the software on all the connected things, the hardware they each use, the communications services via which they connect and the communications hardware over which the communications run. Quickly, there can be 30 or more suppliers in the delivery of this new service.
Building visibility in a connected world
In the digital domain, visibility (being able to recognize and understand any one digital thing talking with another) is key to enabling new capabilities. In any digitized process you require three things: (1) Data that is processed by (2) a ”thing”, e.g. an IoT system (edge device); and (3) connectivity. Effectively, cybersecurity is looking for expected patterns of behaviour (“norms”) by which to make decisions. But as we make more connections to more new things, this scope becomes extremely complex.
At the heart of all cybersecurity, the community needs to be able to answer an increasingly complex question of, “Does this look OK?”, followed by a simple decision. A “yes” allows the process to function, a “no” doesn’t allow it; risk management can be put in place to manage the impact of non-expected or unwanted outcomes. Ultimately to build visibility, the security community needs to prioritize three challenges:
- Standards are still immature globally, and IoT devices often use their own communications languages and communicate in a myriad of ways. Some devices use encryption, which helps protect data but makes it even harder to understand the communication in flow and spot suspicious anomalies. As such, you need cybersecurity that can identify everything and define behavioural norms on an ongoing basis.
- You need to see the whole traffic flow to locate any problems. Specific to 5G, a device or thing always connects to its nearest radio mast, which gives it a network address (an identifier). As the device moves between masts, that identity changes. Protocols ensure communication is seamless to the end device. But unless you have cybersecurity moving with the device as it switches masts, then you must have cybersecurity tools that can re-correlate this traffic together to find the actual thing that is compromised due to cyberattack, or vulnerable to future attack. To manage the risk, you need to track the moving communications flows (both in 4G and 5G), understand what’s communicating with what, and analyze if it is functioning as designed/intended, or if there's a threat.
- Finally, security controls must be savvy to traffic segmentation and prioritization controls. Network segmentation is an architectural approach that divides a network into multiple segments or subnets, each acting as its own small network; this allows network administrators to control the flow of traffic (and prioritize it as needed) between subnets. Cybersecurity tools need to be engineered to understand and align to this process; because 5G allows so many connections, it also allows traffic to be segmented, such as for critical systems or processes to be prioritized (i.e. Critical National Infrastructure resources).
How is the Forum tackling global cybersecurity challenges?
If business and security leaders can understand which entities are involved in the data chain of custody, organizations can identify the weak points and build resilience around them. This requires us to understand that, “Who owns the risk?” is not an easy question to answer today because of the lack of visibility. Clearly, we will need to be able to unpack the complexity and see what's in the digital-process ecosystem to make informed risk decisions and ensure the security community has the capability to answer that question.
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Cybersecurity
Related topics:
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on Supply Chains and TransportationSee all
Isabel Cane and Rob Strayer
November 13, 2025