Cyber impact of conflict in the Middle East, and other cybersecurity news

Cyber experts are increasingly critical in modern conflicts. Image: REUTERS/Illustration
Akshay Joshi
Head of the Centre for Cybersecurity, Member of the Executive Committee, World Economic Forum- This regular round-up brings you key cybersecurity stories from the past month.
- Top cybersecurity news: Cyber plays key role in Middle East conflict; misuse of AI for cybercrime; Portuguese officials' messaging accounts targeted.
- The World Economic Forum’s Centre for Cybersecurity provides an independent and impartial platform to reinforce the importance of cybersecurity as a strategic imperative and drive global public-private action to address systemic cybersecurity challenges.
1. Cyber impact of conflict in the Middle East
The escalation in the Middle East over the past few weeks has highlighted the growing role of cyber warfare in modern conflicts. While military strikes are widely reported, in the background, cyber operations are more quietly taking place.
The impacts extend far beyond the regions directly involved in the conflict, with Europol spokesperson Jan Op Gen Oorth saying he expects to see more cyberattacks against European infrastructure and an increase in online fraud, exploiting the flurry of information circulating about the conflict online, Reuters reports.
Here are some of the reported cyber impacts of the conflict:
- Surveillance networks created: The Financial Times was told that CCTV and traffic cameras had been hacked to create a surveillance network ahead of military strikes.
- Websites and apps hacked: Multiple news websites and the BadeSaba app, a religious calendar app, have been hacked to display messages.
- Medical device company targeted: Iran-linked hackers reportedly seized company data from Stryker, one of the world’s largest medical device companies. The organization stated: "We have no indication of ransomware or malware and believe the incident is contained."
What comes next is unclear, though Adam Meyers, senior vice president of counter adversary operations with CrowdStrike, suggested to Reuters that the current cyber activity may precede more aggressive operations: "CrowdStrike is already seeing activity consistent with Iranian-aligned threat actors and hacktivist groups conducting reconnaissance and initiating DDoS attacks."
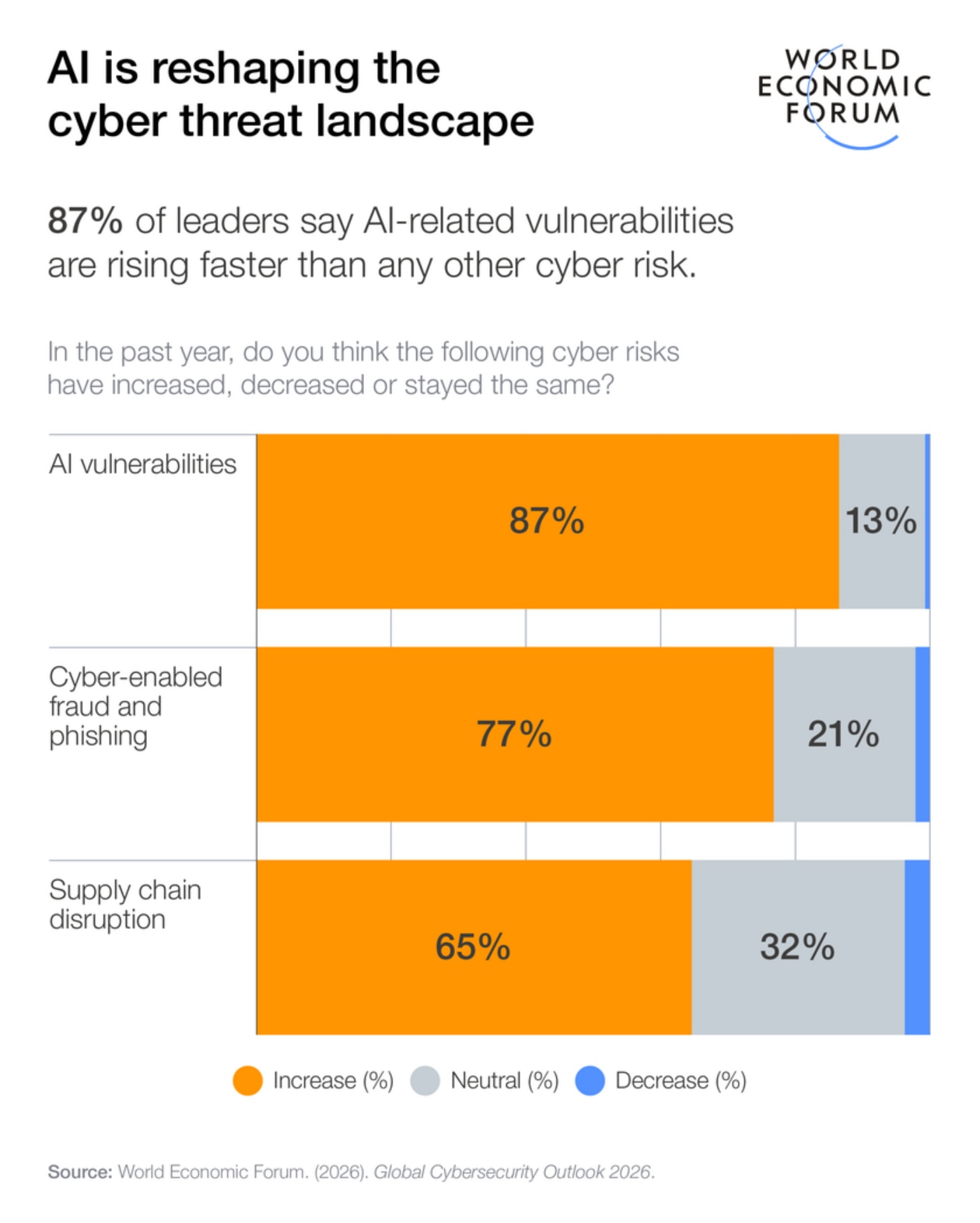
Earlier this year, the World Economic Forum's Global Cybersecurity Outlook 2026 highlighted the significant impact that geopolitical risk has on cybersecurity. The report found that 64% of organizations are accounting for geopolitically motivated cyberattacks such as disruption of critical infrastructure, sabotage or espionage.
2. Misuse of AI for cybercrime
Rapid developments in artificial intelligence (AI) are accelerating innovation across sectors. However, just as these capabilities are opening new possibilities for systems that benefit people, society and they environment, they also present cyber risks.
To help address this and improve transparency within the sector, big tech companies are sharing regular analyses of how bad actors are using AI tools for malicious purposes.
Here are some of the reported use cases of AI for cybercrime:
- Automating scams: OpenAI's recently published threat report highlighted instances of romance scams targeting Indonesian men and another targeting fraud victims, impersonating law enforcement to defraud these victims further.
- Influence operations: The report also revealed large-scale social media influence campaigns that use AI to generate content and distribute it via social platforms.
- Creating code: Anthropic's Threat Intelligence report stated that a UK-based criminal with minimal coding skills used Claude to build and sell ransomware packages online for up to $1,200, outsourcing the technical expertise entirely to AI.
- Infiltrating organizations: Both Anthropic and Google's Gemini referenced North Korean actors using AI models to build false CVs and pass job interviews, to earn salaries with little work or place undercover IT workers at key companies.
Moreover, a new report from INTERPOL found that AI-enhanced fraud is 4.5 times more profitable than traditional methods. Agentic AI systems, the report notes, can autonomously plan and execute complete fraud campaigns from reconnaissance to ransom demands.
"Enabled by artificial intelligence, low-cost digital tools and increased global criminal collaboration, we are witnessing the industrialization of fraud," INTERPOL Secretary General Valdecy Urquiza said in a statement.
The report was released during the Global Fraud Summit, which is being held in Vienna and was organized by INTERPOL and the UN Office on Drugs and Crime.
3. News in brief: Top cybersecurity stories this month
Portuguese officials' messaging accounts targeted: Portugal's national intelligence service has warned that hackers are running a global campaign to access WhatsApp and Signal accounts of government officials, diplomats and military personnel. The actors are tricking users into sharing passwords to access private chats. See how Signal responded to this incident below:
Customer data leaked in telecom hack: The criminal group behind a recent hack on Dutch telecom provider Odido has published customer information on the dark web. Personal data for around 6 million customers was stolen, including names, telephone numbers, e-mail addresses, bank account numbers, birth dates and passport numbers.
Sweden warns energy sector to raise security: The nation's security agency warned the energy sector to heighten its defences following a recent cyberattack in Poland, though no specific threat exists for Swedish infrastructure. The alert aims to make Sweden a harder target, with authorities requesting upgraded security measures.
4. More about cybersecurity on Forum Stories
Why quantum security is a question leaders cannot ignore right now.
Quantum computing is not yet breaking encryption, but the risk is already live. The "harvest now, decrypt later" model means adversaries can capture encrypted data today and unlock it once quantum capabilities mature. In 2024, the US National Institute of Standards and Technology finalized its first post-quantum cryptography standards, signalling the transition is no longer theoretical. Yet many organizations remain unprepared. Migration is a multi-year programme spanning hardware, software, protocols and supply chains, especially where systems last decades. Leaders must align three timelines: how long data must stay secure, how long migration will take and when quantum capability arrives. Find out why quantum security is now a governance issue, not a future curiosity.
Is this how to prepare for an agentic AI-driven future?
Agentic AI marks a real shift in how work gets done inside an enterprise. We’re moving beyond systems that assist humans to systems that are trusted to reason, decide and act on their own. That change is already underway and it’s happening inside core business workflows – not in labs or pilot programmes. An expert breaks down how to prepare for an agentic AI-driven future in this article.
How to prioritize cyber resilience in the healthcare sector.
Healthcare organizations face a growing paradox: prioritizing patient care and digital innovation often leaves cyber resilience underfunded, yet cyber incidents increasingly disrupt care delivery and patient safety. However, strategic digital twin simulations can help leaders test investment choices, reveal hidden trade-offs and identify counterintuitive strategies that improve clinical capacity and digital resilience simultaneously. Read how data-driven decision tools can strengthen governance and protect patient outcomes.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on CybersecuritySee all
David Haber
March 6, 2026