What would a cyberwar look like?

Hard to attribute, borderless, and sudden, cyber threats threaten to erode sovereign power Image: REUTERS/Rick Wilking
This article was updated on 4 January 2020.
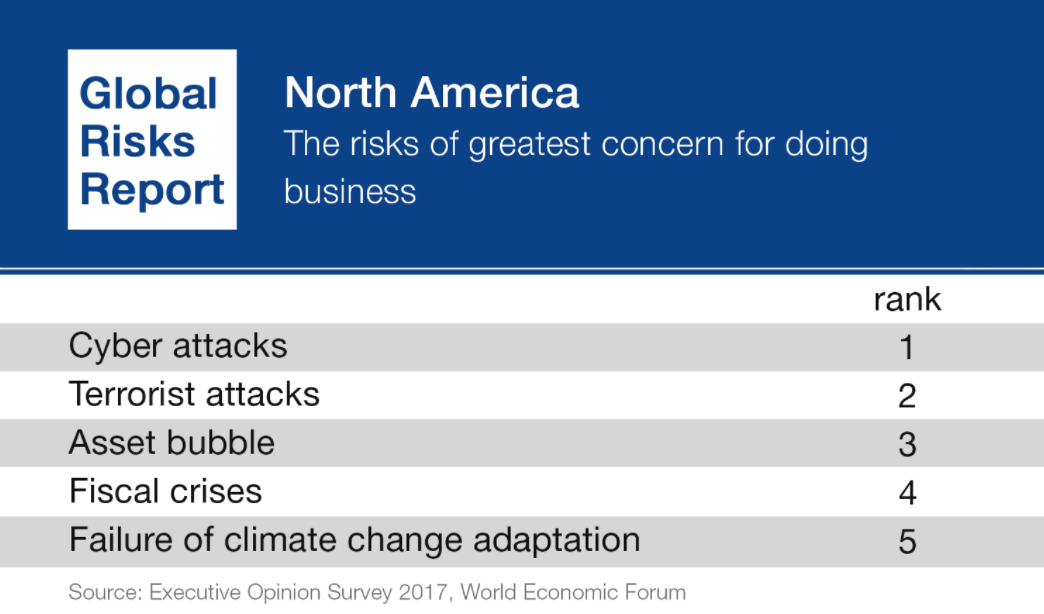
A new year brings new alarms about the prospect of cyberwar.
This time, in the wake of the sophisticated and significant breach of Solarwinds, a network management vendor for most of the Fortune 500 and US government agencies, officials are rattling sabers against a “virtual declaration of war” because of cyberspace “invasions”.
This follows years of similar claims, that governments are attacking civilians in a time of peace, as suggested during the 2018 RSA cybersecurity conference in San Francisco. These attacks aren’t with tanks and warplanes, but with bytes and bots and they are aimed at our energy grids, our infrastructure, and even our private financial and other information.
We’ve increasingly seen reports of cyber incursions, attributed to nation-states, into critical infrastructure and financial systems. We’ve seen further attempts to affect countries’ internal political institutions. Nations have also been reported to be stockpiling software and network vulnerabilities, purportedly to use for espionage or in the event of an internet-enabled conflict.
Even if some claims of cyberwar are overblown — and notions of a looming "cyber-geddon" almost certainly are — the rapid adoption of new technologies as a mechanism of statecraft create ambiguity and give rise to risks that we need to understand. Along with this rapidly changing technological environment, the international legal and normative environment can be best described as muddy. While states and international bodies often say that international law applies in cyberspace, very few have been able to point specifically to what that means and a consensus on case-by-case applications is by no means assured.
So, before worrying that we’re in a cyberwar, the first step should be toward clarity about what cyberwar may look like and what governments, institutions, companies and citizens can do about it.
What is a "cyberwar?"
The reason the idea of cyberwar has led to such alarm is that it's new — and ambiguous. As with many new technologies, it leaves us without norms and accepted definitions that clarify intentions, actions and consequences. There is even significant controversy among leading nations regarding whether the law of armed conflict should be applied to activities on the internet.
Muddying the waters further, espionage, crime, and hactivism have been lumped together, in a way that they are almost never combined in the physical world. All are sometimes defined as cyber war either out of semantic lassitude or as a way to magnify the supposed threat.
In order to take the threat of cyber war seriously, we should recognize that not all detrimental activity online should be called "cyberwar" just as not all actions between states are defined as "war."
A reasonable definition must take into account specific forms of aggression and intended results — "cyberwar" is not crime, it is not espionage, it is not propaganda and it is not terrorism.
Thanks to ambiguity in this area, definitions of cyberwar tend to be vague descriptions of "damage to computers or networks" — another way of saying "things we'd prefer not be done on networked space." Those notions lack sufficient rigor to be of help. A more specific definition of the aggressive action we seek to avoid is necessary.
The term "cyberwar," therefore, is best understood to refer to an act of aggression, committed through a digital network, meant to cause damage in the real world, either to civilian or military targets, in order to force a sovereign state to act or refrain from acting.
As a corollary, the actor here must be another state, since similar actions by an individual would likely be called cyber terrorism in the same way that a non-state actor who attacks a nation's physical assets is termed a terrorist, regardless of the weapon used.

Are we engaged in cyberwar?
It helps to examine instances of aggression in the digital space to put cyberwar into context. The most successful cyberattacks we know of were Stuxnet, used against Iran, and the NotPetya attack on Ukraine.
Stuxnet, a computer worm, was the first widely known example of malicious code actually causing real-world damage (albeit minor). Unlike the previous instances of digital incursions, Stuxnet was actually meant to have an effect similar to what a nation would once have used kinetic warfare to do: knock out an enemy's infrastructure or weapon-making capacity. Because of the sophistication of the malware and its clearly geopolitical, rather than criminal, purpose, the attack has been attributed to a nation-state (or multiple nations acting together).
Another example of warlike code is the NotPetya "mock ransomware" attack that devastated Ukrainian businesses. At first, that attack seemed to be a sophisticated ransomware operation — where criminals take control of an organization's network and threaten to erase or encrypt critical data unless they receive a pay-off. However, because NotPetya went straight to damaging systems and deleting data, rather than waiting for a pay-out or stealing data, the malware is viewed by most researchers as a weapon in the ongoing war in Ukraine.
Other famous instances that recur in the cyberwar conversation, like the 2007 cyber attacks against Estonia that were attributed to Russia, or alleged Chinese intellectual property theft in the United States, are really more akin to vandalism and espionage in their methods and effects.
While all those cyberwar and potential-cyberwar examples may seem minor compared with traditional warfare, they are signals of a troubling turn in nations' cyber-statecraft.
First, those attacks — hard to attribute, borderless, and sudden — show how cyber threats erode sovereign power. After all, from the Treaty of Westphalia to the digital age, sovereigns have held some very basic, unchanging attributes. At the very least, those attributes include the ability to secure a nation's borders and to have some modicum of control of the activities within those borders. When an aggressor has the ability to use borderless networks to launch attacks that can't be intercepted or prevented, those attributes and therefore sovereignty itself are called into question.
Second, the use of digital networks to carry out attacks significantly threatens innovation. After all, the internet has been an unparalleled engine for growth. But real or imagined cyber threats use those same networks. The temptation, then, is to limit connectivity or to set up networks of walled gardens in an attempt to ensure better control or security.
What can we do about it?
First, it is important to have some perspective on the risk itself — most of the attacks that hurt ordinary people, companies and organizations are motivated by crime, not geopolitics. Therefore, supporting a trusted and safe internet goes a long way toward alleviating the worst and most common risks.
Additionally, the same governance and best practices are effective against most threats, regardless of the actor — whether in a time of war or a time of peace, one must close his door and avoid inviting thieves in.
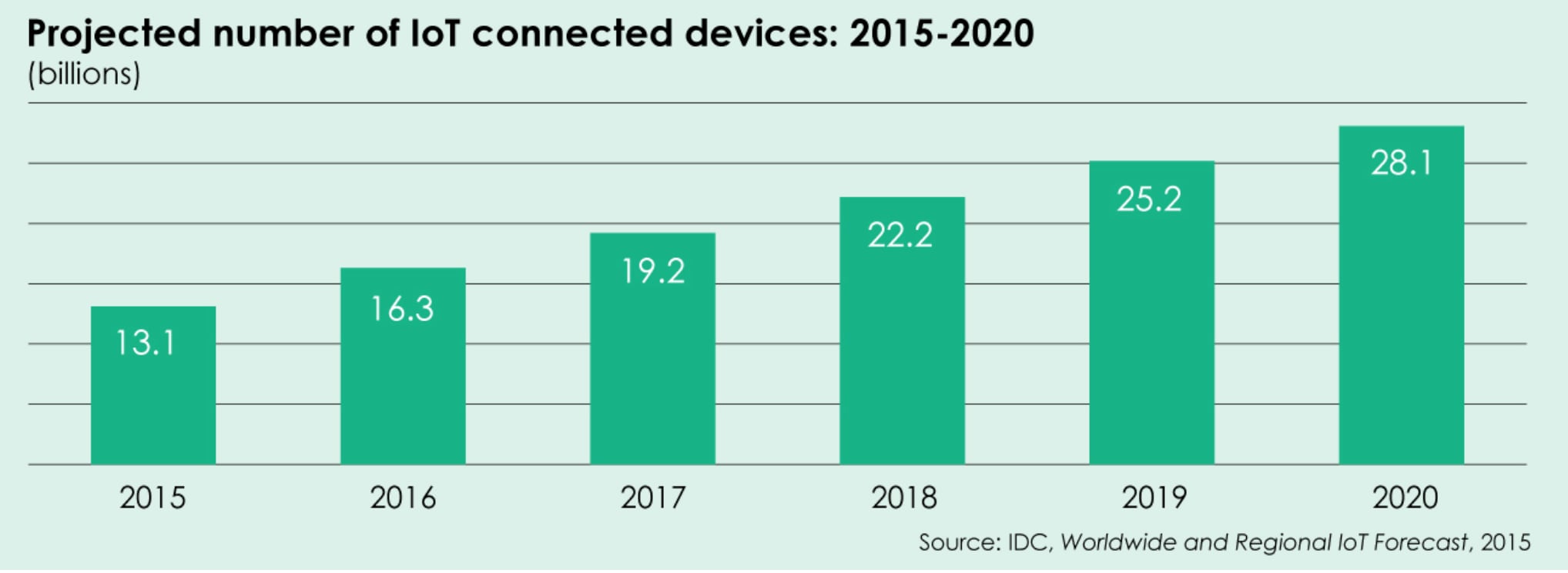
The World Economic Forum's Centre for Cybersecurity is dedicated to building the partnerships, tools, and capabilities necessary to meet cyber threats. The Centre will act against cybercrime especially, and provide a shared space to understand new areas of threat, such as the internet of things or artificial intelligence. The Centre is also neutral platform for governments to work with the private sector to shape cybersecurity governance.
Importantly, there are a host of efforts to create a culture of security and trust and to bolster or develop norms against cyberattacks that have so far been lacking. It might be said that there are even too many competing efforts to shape the same result. What’s important isn’t the number of attempts, but rather the will for all actors — governments, companies and citizens — to take part in shaping our shared digital culture together.
After all, digital spaces, lacking borders and with guarantees of anonymity, are rife with the potential for misunderstandings, especially between adversaries who may not be fully apprised of what other countries' secret hackers are up to.
The more we can do to improve security generally, to stop cybercrime and thereby decrease the signal-to-noise ratio for attribution, and to work together to shape norms against using digital networks as arenas of combat, the less likely cyberwar will be.
Don't miss any update on this topic
Create a free account and access your personalized content collection with our latest publications and analyses.
License and Republishing
World Economic Forum articles may be republished in accordance with the Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International Public License, and in accordance with our Terms of Use.
The views expressed in this article are those of the author alone and not the World Economic Forum.
Stay up to date:
Cybersecurity
Related topics:
Forum Stories newsletter
Bringing you weekly curated insights and analysis on the global issues that matter.
More on CybersecuritySee all
Julie Iskow and Kim Huffman
November 11, 2025